Hello everyone,
the EU General Data Protection Regulation (GDPR) went into effect on May 25, 2018, exactly 2 1/2 years ago.
Especially Art. 17 - the right to be forgotten - issues a challenge to software systems.
In this thread I would like to collect your solutions in conjunction with the Axon Framework and the Axon Sever and/or an embedded event store.
Thanks for sharing your ideas and solutions.
Kind regards
Oliver
3 Likes
Hello Oliver,
Event Sourcing mandates that the state change of the application isn’t explicitly stored in the database as the new state (overwriting the previous state) but as an immutable series of events. You should not delete these events and/or change the content. This way you don’t lose any data/information. Everything that happened in the system is stored. Information is far more valuable than the price of the storage these days, Don’t throw it away 
But, some attributes of an event should not be read by all consumers, and we should be able to delete them, without touching the event store (series of events). One of the common solutions to this problem is to encrypt the sensitive attributes, with a different encryption key for each resource. Only give the key to consumers that require it. When the sensitive information needs to be erased, delete the encryption key instead, to ensure the information can never be accessed again. This effectively makes all copies and backups of the sensitive data unusable. This pattern is known as Crypto-Shredding. The Crypto-Shredding pattern is of course only as good as your encryption and your key management practices and in my opinion a better option than just running the delete on SQL table (do you delete all the data really - what about logs?)
Axon provides a commercial module Axon Data Protection module (https://axoniq.io/product-overview/axon-data-protection) for this purpose.
Best,
Ivan
2 Likes
Thanks @Ivan_Dugalic,
I’m aware of the GDPR module and of course it’s one way to address this issue.
I just would like to know if there are other solution in conjunction with Axon Framework.
Regarding crypto shredding I read that it might not be GDPR compliant. Do you have so newer sources about this topic?
To be more concrete here some patterns and I would like to know if some people implemented them with Axon.
2 Likes
Regarding crypto shredding I read that it might not be GDPR compliant. Do you have so newer sources about this topic?
At the time we introduced the Axon Data Protection Module (back then called the GDPR Module), we had a security expert work on it. He also checked all the regulations and options out there, finding crypto shredding to be a fine fit for the problem at hand.
So, do we have newer sources? No. At least, not that I currently know off.
Legal stuff is nothing a software engineer wants to deal with, right?
With my knowledge I cannot decide what’s compliant and what’s not compliant… I just can collect alternative solutions which might be an option to be GDPR compliant.
From a software engineer’s point of view crypto shredding is the most promising approach…
Hi,
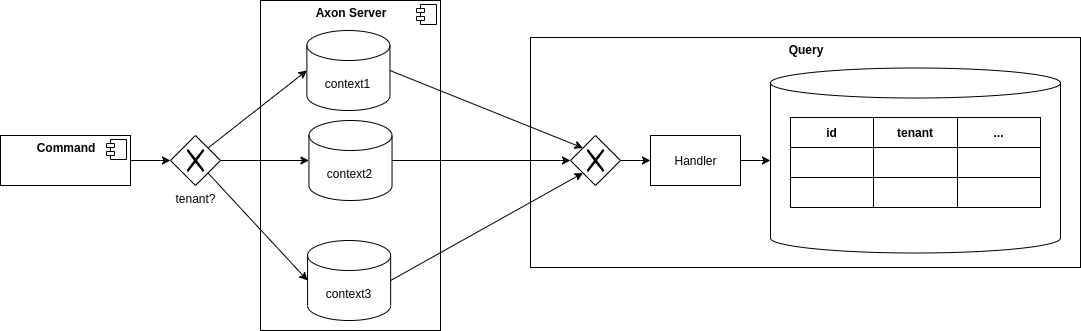
one alternative approach that came to my mind recently would be to fan out events per tenant/user to different contexts and flag them in the query projections.
That would allow to simply delete the context of the tenant/user and clean up the view-projections without touching events or data of other users. However I don’t know if that pattern would scale well with axon framework for a large number of tenants/users (meaning a large number of contexts to maintain).
Best Regards,
Jakob